Each wallet of any cryptocurrency has its own seed. It consists of a sentence consisting of a number of words. The seed is extremely important, which is why it must be stored with great care, perhaps on several paper copies offline, as it is essential to recover the funds kept in the wallet.
However, there are different types of seeds belonging to real standards, so as to allow the user to recover their funds on different wallets. If, for example, Electrum or Coinomi were to disappear one day, how would it be possible to recover funds without a well-defined standard?
For this reason in recent years have been defined some well-specified standards of seed to safely store their private keys.
Summary
Seed: a phrase to restore everything, anytime, anywhere
Most of the wallets used to offer the possibility to make a backup of the funds through the seed. It consists of a random string of words, usually 12, but can also be 18 or 24 words. It is more or less like a phrase like that:
“inspire october ten crop warfare wink game regular alley mimic anchor extra”.
A sentence of such composed words does not make sense, but it will be the only way to retrieve the funds of the associated wallet, regardless of how many transactions have been executed and how many addresses have been generated.
Once transcribed on a sheet of paper or learned by heart, the SEED (except for loss or theft) will always allow you to retrieve the bitcoins on the associated address. Whether the computer on which the wallet is installed, is uninstalled or destroyed, the SEED will always allow you to recover funds.
How can the seed work to recover lost funds?
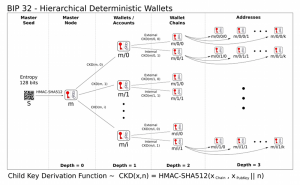
The merit is of the cryptography, in particular of the concept of the hierarchical deterministic wallet, which, thanks to the use of some mathematical functions, allows users, starting from the seed, to recover everything. In fact, it translates the seed into a Master Key, from which all the other keys will be derived in a deterministic order. Just as in the real world you are not bound to the use of a certain calculator to perform a mathematical operation, not even the seed is therefore bound to the specific software of a given wallet.
BIP32, BIP39 & BIP44
The recovery procedure, however, is not too obvious, as it is necessary to make some distinctions based on the standard of seed adopted. There are several, including BIP32, BIP39, BIP44 and also BIP43. Typically, most cryptocurrency wallets use the first three.
BIP32 was the first seed standard for hierarchical deterministic wallets. They are wallets that can be shared partially or entirely with different systems, each with or without the possibility of spending coins.
BIP39 and 44, on the other hand, are a more recent form of standardization of a specific list of words (passphrase) for a given language. This standard also includes the process of transforming those words into a hexadecimal 512-bit SEED, which is the real SEED needed to generate the HD BIP32 wallet. In detail, the BIP44 has introduced the possibility of using multiple accounts.
So any wallet that shows the words “BIP 32/39/44 compatible” will generate a passphrase of 12 to 24 words that will be used to generate a deterministic 512-bit seed. The latter will then be used to create in a deterministic way a BIP32 master key. Finally, from it, the daughter keys will be created according to the method reported in the specifications of BIP39 or 44.
Ian Coleman Code Converter
However, the use of different seed implementations in the main wallets can have some negative repercussions. For example, the Ledger Nano S hardware wallets support SEED BIP39 and 44, idem Trezor. Electrum, on the other hand, uses BIP32. MultiBit supports both BIP32 and BIP44, while Eidoo supports BIP39.
As a result, some wallets such as Ledger use a 24-word passphrase. Others, such as Exodus, can read a 12-word passphrase. Obviously, in these cases, it is not possible to insert only the first 12 words, as the system would not work.
For this reason, therefore, you may need to convert your seed BIP39 or BIP44 in the Master Key BIP32, using some generators, such as the one of Ian Coleman. The latter, among other things, can be run offline to maximize security.
Using this tool, in fact, you can get all the information you need to recover the funds associated with the wallet by simply typing the seed. First, the application will retrieve addresses and private keys, which can be used to retrieve funds with Electrum or any other portfolio that allows the import of private keys.
Secondly, the extended BIP32 key and its Master Key will be shown, which can be used to retrieve a wallet using Electrum, for example.
How is this possible?
To understand how a passphrase works you need some basic knowledge about bitcoin storage. When a user receives bitcoins, they are associated with a certain address. This address is a derivation of the public key, which in turn is a derivation of the private key.
Therefore, the wallet first generates a private key, from which it will then obtain a public key that will finally be transformed into an address.
A simple backup system for bitcoin in a wallet could consist in transcribing the private key into an encrypted file. The private key is a random string of characters, similar to this one:
“L3GrBerZZXtTDcAVNiULbN84UVGjX7ezypSCsYYroBdQDDKKX1E53”.
However, it is strongly recommended not to reuse your address for privacy reasons. For this reason, the last wallets create a new address every time you want to receive bitcoins. Therefore, to back up the received bitcoin, you would have to transcribe all the private keys generated from time to time. In fact, this solution is very uncomfortable.
Fortunately, in 2012 the developer Pieter Wuille created the BIP32 specification at the base of the hierarchical deterministic wallets. Together with it, Pieter created a mathematical function to create a master key from which to derive all other keys in a deterministic way.
For example, given a master key A, it will always generate the keys a, b, c, d and so on, always in this order. Subsequently, some developers have created additional tools to derive the master key from a seed of 12, 18 or 24 words (BIP39) and to add support to several accounts (BIP44).
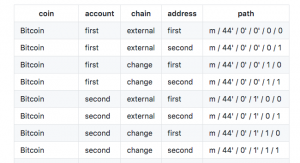
In the case of BIP44, therefore, you will have for example that, given the Master Key A, it will generate accounts a, b, c, each of which will have its own keys 1, 2, 3. A very interesting feature that allows the wallets to ensure the privacy of users against the data mining of the blockchain. Over the years, in fact, analysis mechanisms have been developed to trace the identity of users by tracking transactions and addresses visible on the blockchain. With BIP44, therefore, they become ineffective.
The seed, therefore, is more than just a recovery key, as it also allows you to trace all transactions and addresses. Of course, this system also works on other cryptocurrencies, not just bitcoins. You can then get keys for litecoin, monero, ethereum, etc from the same seed. For this reason, multi-currency wallets such as Exodus, Jaxx and others, can store multiple cryptocurrencies using the same seed.
Offline is always more secure
However, there is one last problem. As much as wallets are Open Source, PCs are protected from malware, browsers are equipped with anti-phishing filters and so on, there is always a slight chance that someone can steal the seed during the generation phase.
There are in fact tools that record the activities performed by PCs. Moreover, computers do not always have an adequate level of entropy in creating a random sequence of numbers, especially if disconnected from the network.
For this reason, you can perform all these operations offline and use additional variable parameters chosen manually by the user. Once the seed is created, one of the best storage solutions is offline storage, perhaps on multiple sheets of paper or metallic seed keepers.


