One of the trends in recent years that criminals have adopted as a strategy to obtain Bitcoin from victims is that of sextortion: the user receives an email requesting BTC in order not to publish allegedly explicit images.
But what does such an email look like?
This type of attack involves an e-mail with an unusual subject line and sender, usually self-explanatory, as in this case: “I got you on tape”, a clear reference that the victim was somehow filmed.
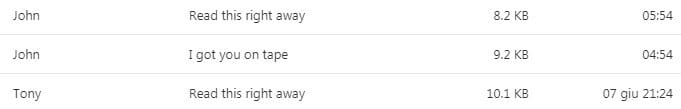
Usually, this type of e-mails are filtered by the e-mail service and are automatically sent to the “spam” mailbox, but this does not always happen and hence they can also be found in the inbox.
At this point, the victim, out of curiosity or concern, opens the content of the message.
The e-mail starts warning the victim that his/her network has been hacked and that it has logged his/her porn video sessions: in fact, the criminal claims to have hacked the router with a code that activates the webcam recording every time an adult site is visited.
The content provides technical aspects about how the system works and how this is not tracked by antivirus because it doesn’t steal anything but only records the video, which is not harmful in itself.
At this point the criminal initiates the sextortion, trying to extort Bitcoin from the victim, in this case, 0.055 BTC (about $500), providing an address divided into 2 parts. The same criminal instructs to merge the two codes to get the full address.
This methodology shows that the criminal can use an address generator to send different emails with a different address, also to escape tracking: if they always use the same address this would end up more easily in an exchange blacklist making it difficult to liquidate the funds.
Interestingly, the criminal invites the user to search for the name Paxful, a clear reference to the relative exchange, in order to obtain the necessary bitcoins. The user has 72 hours, i.e. 3 days, to send the BTC and avoid that the explicit images are made public.
The message closes with two notes: to respect women and to focus on other healthier activities such as working out, maintaining a healthy diet, learning something new.
What to do in the case of sextortion?
After receiving a message like this, simply trash it, before opening the content, because inside it there could also be some harmful links that could lead to some harmful websites.
In fact, the threats are fake and the criminals are not really in possession of compromising images. It is basically just a bluff to steal bitcoin.