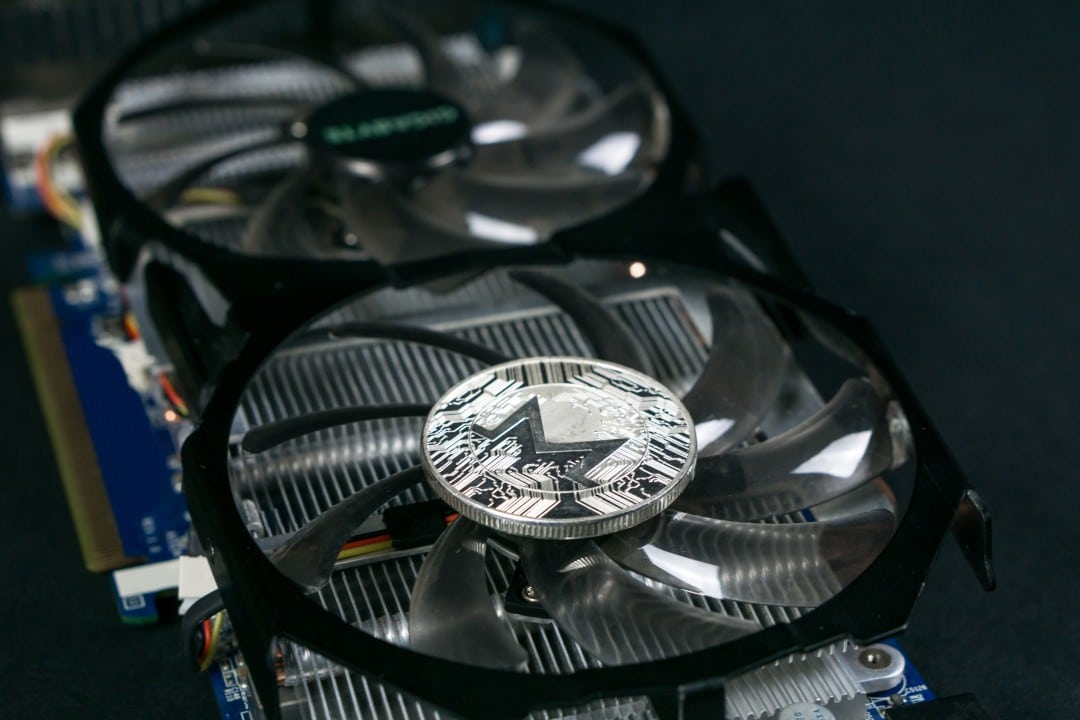
Recently, Cylance’s team of researchers wrote a detailed report about the anomalous behaviour of an audio file (WAV file) which concealed all the necessary to mine the Monero (XMR) cryptocurrency without the user’s knowledge.
All this was discovered by analysing an audio file with a WAV extension containing several codes including Monero’s XMRig, which is the one that allows to mine Monero with the CPU; there were also other audio files containing codes to remotely access the victim’s computer.
Indeed, through techniques of obfuscation of data within multimedia files (steganography) like videos, audio and images, it is possible to include a small amount of information, such as lines of malicious code, without the end-user noticing it at all.
As is well known, criminals prefer to mine the Monero cryptocurrency because it guarantees a high level of privacy and hence it is used both for mining using the victims’ hardware and as a payment for ransom, with the result that the amounts and balances cannot be traced.
There have been, however, cases in which it has been possible to get rid of malicious codes and destroy them effectively, consider what the French Gendarmerie did when it destroyed a malware that mined Monero.
These techniques, which are very advanced, are also difficult to identify and discover because they can hide in practically any file and if the user does not have the right tools, such as a good antivirus, it is difficult to prevent the attack. Many times the virus is discovered following significant problems with the computer, such odd behaviour, which can be, for example, the slowing down of the computer, which is the result of the malware exploiting the CPU power in an exorbitant way, making the PC practically unusable.
As usual, it is always advisable to check the files so as to exclude potential unwanted problems. Moreover, downloading multimedia material from unsafe sources could also lead to the downloading of extremely harmful viruses and malware, in fact, part of the virus flow passes through emails that with special devices can induce the victim to download attachments or to click and follow harmful links without their knowledge.