Cryptocurrency and Identity Management: How Blockchain is Changing the Way We Verify Identity
Data security and privacy have become hot topics over the past few years. With more and more companies being exposed for how they use customers’ identities and data, people are looking for alternative and better solutions.
The blockchain is also offering new solutions on how to store and use your identity, giving you greater control and power over it. Here are a few ways that the blockchain is revolutionizing how we store and use our online identity.
Summary
Current problems with digital identity
In the world of crypto, when you trade cryptocurrency, you are fairly anonymous, but you are still identifiable and verified through the blockchain. However, this technology doesn’t expand to many other industries, and this has caused numerous problems.
Security
The biggest problem with identity and data storage solutions today is that they are centralized and hackable if you have the time and the right tools. Data breaches are all too common, and with so much information stored in one place, it’s easy to steal tens of thousands of identities in a single breach.
Lack of access to identity
Many probably don’t know that over 1.1 billion people across the world do not have any proof of identity. This is due to limited access to the right resources, the countless pages of information you need, and a lack of money to pay the fees associated with gaining an ID.
Fraud
As already mentioned, identity theft and fraud is all too common nowadays. With so much personal information so readily available, accessing another person’s identity and using it is frighteningly easy.
Decentralized identifier
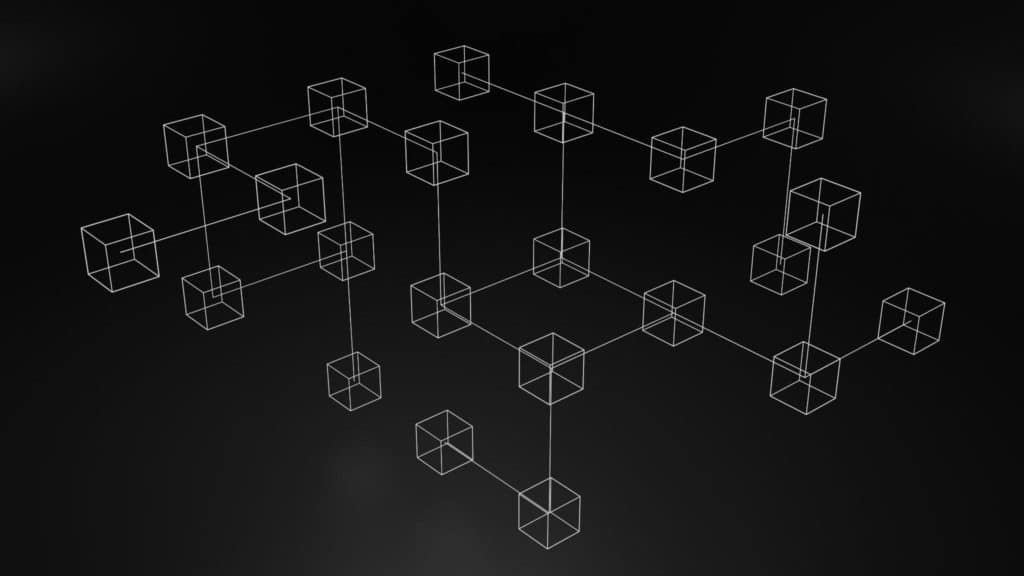
The blockchain can transform how we create and verify an identity by using a Decentralized Identifier (DID). Users can sign up for a self-sovereign identity on a data platform and then create their own DID.
A DID is accessed using a private-public key, meaning only those with the key can see and use your identity. A DID can be filled with credentials and identifying markers that can be used for everything from proving ownership of an item or accessing your gaming account.
The blockchain and cryptography then ensure the safety and security of your DID. The public key associated with your DID can be used to verify your identity, and as mentioned, the private key gives you access to the messages associated with the DID.
A real-use case would be a user providing a QR code to an identifier, which would then prove their identity and allow them to access a particular service. The identifier provides proof of ownership of an identity and credentials and will check if it’s related to a DID.
How the blockchain & DID improve digital identity
The blockchain is completely transforming how we store, access, and share data. It has given us far more control and security than ever before, and is almost certainly the future of data storage.
Security
In simple terms, the blockchain is highly secure because of how it’s designed. Data is placed in a block, and when another block is added, the previous block becomes more secure. The blockchain is also unhackable and unalterable, meaning that once your data is secured, it’s practically secured forever.

Privacy
Blockchain encryption and digital signatures ensure that your data remains your own and cannot be seen or used by outside parties without your knowledge. Considering all the public discourse about data privacy, this will undoubtedly be a very popular development for many people.
Integrity
A blockchain-based identity verification system would allow for an immense amount of flexibility for maintaining identities across all of its nodes. The continuous updates and verifications of all identities across the chain will also make it far more reliable and trustworthy for all users.
A blockchain network doesn’t operate on a single point of failure. This means that hackers or data thieves would have to go through a tremendous amount of work and processes to access the information they wanted.
Simplicity
Finally, a blockchain identity verification system is incredibly simple to use and access. There are clear sets of rules and processes, and therefore you can do away with red tape and the normal stumbling blocks associated with traditional systems.



