Yesterday, January 9th, the Ethereum Classic team organised a call on Discord to discuss the 51% attack that occurred a few days ago and to find possible solutions for the blockchain.
On a Medium post, Donald McIntyre, Business Developer Manager of ETC, stated: “we will not reorg the chain or revert the events on chain under any circumstance.”
Despite this decision, the 51% attack on the Ethereum Classic chain will result in the creation of new security procedures, including:
- Creation of a monitoring and alerting system for ETC so that the attacks can be detected sooner which will allow to find solutions quickly;
- Recommending users to wait at least 2500 to 5000 confirmations depending on the transaction;
- Studying a way to implement deep-reorg protection;
- ECIP1043: to set a limit to the maximum size of DAGs;
- Waiting for ETH to switch to ProgPoW or PoS, making ETC the main chain using PoW;
- Changing the PoW algorithm to become the main chain in the new PoW niche. The two options under consideration are ProgPoW and Keccak256 (ECIP1049).

Obviously, the Ethereum Classic team also analysed what went wrong and why this 51% attack happened.
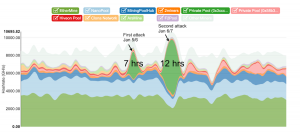
The miner responsible for the attack was identified as Private Pool 0x3ccc8f74 on GasTracker.io and had started the attack on January 5th, then continued the next day with another, more prolonged, attack.
Among the reasons found by the Ethereum Classic team, there are only external factors: the 51% attack would not have been caused by internal ETC vulnerabilities.
Among these, the fact that ETC is vulnerable to 51% attacks because of the Proof of Work, like all other blockchains using this consensus mechanism, and that an insufficient number of confirmations for transactions was required.



