One of the primary objectives of cryptocurrencies is certainly to ensure anonymity and privacy. Among the one that achieve these goals the closest are Monero, Zcash, Beam and Grin. But what are the differences between these four cryptocurrencies?
Anonymity or presumed anonymity is one of the most controversial elements of the crypto world.
Monero is one of those cryptocurrencies that aims to guarantee it 100%. But the Monero project does not completely keep its promises in this regard.
Monero
The cryptocurrency, launched in 2014 under the name BitMonero, relies on a technology called Cryptonote.
It is a Proof of Work algorithm different than that of Bitcoin. In order to make the operations on its blockchain anonymous, the method adopted is that of the “Ring Signatures”.
It is a digital signature that can be created by anyone and in which each user has the key. A person can then put the electronic signature anonymously in a message or document on behalf of a “circle” of users. The members of the “circle” are chosen by the author of the signature and are not necessarily informed about the operation.
The strength of Monero (XMR) is therefore based not only on decentralisation but also on its secrecy, which allows carrying out transactions that are theoretically untraceable by an external agent. If, for example, bitcoin operations are publicly recorded on the blockchain, in the case of Monero’s ledger, the information is not accessible to everyone.
Pseudo anonymity
Having said that, the platform is not working perfectly. In fact, some flaws in the system have been found with regard to privacy and security.
The team of about 250 experienced cryptographic manufacturers is trying to remedy this.
Monero’s trick to ensuring anonymity is to confuse those who want to trace the source of the operation, by mixing the origin of the operations performed on the platform.
But last year a group of academics published a long memo in which the myth of anonymity is partly dispelled. It lists the weak points of the structure in terms of how it was conceived and the problems that could arise if someone discovered the trick.
Latest updates and improvements
Another strong point of Monero is the protocol that – contrary to what happens with Bitcoin, where you need to have very powerful and specialised PCs – allows traditional computers to compete with the mining giants.
At the same time, the anonymity of operations requires the use of more space for “public” operations. As a result, an XMR transaction is 25 times more voluminous than a BTC transaction and was also just as expensive.
However, after the latest updates, including Bulletproofs, costs have been reduced by 97% and comparing prices today, Monero has become cheaper than Bitcoin.
Monero: Scalability needs improvement
Progress has also been made in terms of workload, but scalability remains one of the weaknesses. The memory of operations has been reduced from the original 18.5 KB and Monero’s engineers are trying to find ways to increase network capacity.
The problem is that the Ring Signatures system adds data to operations, increasing the load on the blockchain (48 GB at the moment). Each operation requires 14 KB, 25 times more than Bitcoin.
The upgrades implemented by Monero’s team should lead to a scalability improvement of up to 80%, which would result in a “proportional reduction in commissions”. However, even if this were the case, the memory would be 5 times higher than that of Bitcoin.
Monero, Beam and the differences with Zcash and Grin
To strengthen the protection of data and identity of its users, Zcash uses a different type of system than Monero. The technology on which the crypto is based, founded in 2016 by the cryptographer Zooko Wilcox, is called ZK-Snarks and allows to secure the operations carried out on the network.
Two types of addresses are available with Zcash:
- z-address (private addresses);
- t-address (transparent addresses);
Therefore, 4 types of transactions are possible
- Private: z-address -> z-address
- Deshielding: z-address -> t-address
- Shielding: t-address -> x-address
- Public: t-address -> t-address
Using z-addresses is considered expensive, both for the wallet and for a z-cash node. Therefore, private transactions are used sparingly.
The crypto uses a complex code system that allows hiding transactions, revealing only the parts that are strictly necessary. The cryptographic principle in question is called the “zero knowledge” protocol.
Thanks to the Zero-Knowledge proof, when the operations in ZEC – the reference token of Zcash – are recorded on the blockchain they are automatically encoded and deleted from the history and therefore are no longer available. The user proves they have a token when the exchange is made and then it is destroyed to leave space for a new virgin token that will be actually used in the operation.
There is no link between the old and the new token (which doesn’t have “memory”) and therefore between the original token and the user. The only way to access detailed information, such as the amount of the transaction or the identity of the buyer, is to have a key and a password, but these are known only to the issuer and receiver of the single transaction.
Even for Zcash, one aspect that can still be improved is that of scalability. The blockchain weighs about 19 GB, while each transaction requires on average 5.3 KB. This is lower than Monero, but 9 times higher than Bitcoin.
Zcash therefore keeps its promises regarding anonymity, offering features that guarantee privacy but are heavy. Scalability is more satisfactory than Monero’s but there is room for improvement.
An open system but one that provides remuneration
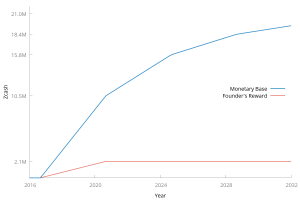
The Zcash code is open source and – as for Bitcoin and other digital coins – the monetary supply is fixed: there will never be more than 21 million tokens. As far as mining is concerned, a block of Zcash is extracted every 2.5 minutes. In the case of Bitcoin it takes about 10 minutes.
A substantial difference with the most popular and capitalised crypto such as Bitcoin, Ethereum or Monero, is that although it is based on an open source code, Zcash is not a completely “anarchic” project, but has its own hierarchy.
The goal of its founder is that one day Zcash will be financially supported by people who serve the interests of all users in a fair manner. These people will be part of a foundation. Some of the founders of Zcash can freely decide to contribute to the “Zcash Foundation” that will be launched in the future.
Therefore, Zcash can be considered as a “free” company, which provides remuneration for its investors, managers, directors and employees. All this is financed by a 10% tax levied as a reward for mining: Founders reward.
Beam, what differences?
For its part, Beam is based on a relatively new protocol, launched in August 2016 and called MimbleWimble, which guarantees both anonymity and scalability. It focuses more on these two aspects than on programmability. According to its creators, it is able to increase in scale according to needs and availability.
A bit like Bitcoin, Mimblewimble is based on the concept of “transactional output”. Each operation consists of an input and an output. The peculiarity of the Beam model is that each input represents the output of a previous operation, in a sort of indefinite chain.
For this reason, the exit of the unspent transaction (UTXO) becomes fundamental: it is a fragment of the currency kept in the blockchain without being spent. It is scattered over multiple transactions and represents the tokens in circulation.
Techniques to ensure scalability and anonymity
The “Coinjoin” technique allows these operations to be mixed, integrating several of them into one. Two input operations can lead to one output operation and vice versa two inputs can lead to only one output.
Coinjoin is applied to all operations performed on the blockchain, so a block of MimbleWimble actually contains a single large transaction. The bigger it is, the more difficult it becomes for an external person to know which is the output corresponding to the entry.
Moreover, thanks to the “Confidential Transactions” system, the sum, the buyer and the seller of the transaction are hidden and addresses cannot be found by examining the system. The method involved is called homomorphic encryption.
Privacy guaranteed by default
Each user has a personal key to access the output of the UTXO (unspent transaction output) transaction. In summary, to use Beam’s words, “privacy is guaranteed by default”. There are no “open” operations. If you try to examine the blockchain from the outside, you will not find any useful information.
Another technique is the “cut-through transaction”. Large trades that are older are merged at some point. In this way, all the intermediate states of UTXO are eliminated and only the final unspent outputs are stored on the blockchain.
This allows freeing up space on the blockchain. The ledger does not grow in size with the number of operations, but with the number of UTXO. Such a system offers advantages in terms of scalability. The protocol is designed to stay small, making the workload “lighter”.
It is estimated that the size of the Beam blockchain is 30% of that of Bitcoin at the moment. When Beam reaches the scale of the most popular digital currency in the world, its blockchain should not exceed 70 GB. Not to mention the ongoing adjustments that can still be made.
Some sacrifices in the name of scalability
To achieve a scalable and confidential blockchain, MimbleWimble renounces some useful bitcoin functions, such as transaction programmability. While Bitcoin uses a “script” system to validate the expenses of transactional outputs, allowing the programming of smart contracts, the Beam protocol does not.
According to one of its creators, the mathematician Andrew Poelstra, it can still be remedied by inserting “scriptless scripts” thanks to ingenious systems with multiple signatures. The scripts would therefore not be executed on the machines of the network nodes, but on those of the users involved in the operation.
The second feature that we don’t find in MimbleWimble is offline payments. In the protocol there is no address and the construction of the operation must be done on the interaction between the two parties. This has an impact on the user experience, but also on its privacy because you need the IP address. To solve the problem, the Dandelion solution was proposed, a protocol designed by Giulia Fanti of Carnegie Mellon University.
Grin: What are the differences with Beam?
Grin is also a protocol based on MimbleWimble, but what are the differences with Beam? Grin is the original application of the protocol named after the Harry Potter saga. Its launch took place on January 15th, 2019.
It is a “lighter” application and a more “reserved” design compared to Beam, in the sense that it only offers the fundamental functions and does not aim to compete with bitcoin. There is even an exhaustive list of things it does not do.
But the main difference is the philosophy behind the two projects.
Grin is more anarchic, while Beam has a more commercial aspect. The first is in fact an open source project developed over the years by several programmers, most of whom have preferred to remain anonymous. The second is instead produced by a defined team that is promoted on a dedicated website.
Another clear distinction concerns monetary policy. Beam’s monetary supply is limited, while in the case of Grin an infinite number of tokens can be issued (an average of one grin per second is released). The strategy in the latter case is therefore inflationary.
Beam’s strategy, on the other hand, follows the deflationary policy of bitcoin, which aims to reduce the emission of new tokens over time. Beam’s vocation is to become a store of value, while Grin does not aspire to that and is “satisfied” with being an exchange tool able to offer privacy and scalability.



