Such a backdoor, if it existed, could allow the forced participation in a given mining pool, the routing of block rewards to a given address, the boycott of blacklisted pools or the implementation of a kill-switch.
Bitmain‘1s reputation would be destroyed and its earnings would drop significantly if a backdoor were to be found. While the first two types would be obvious, the other two could be more discreet. Having said that, it is difficult to imagine that such systems would go unnoticed.
This, however, is not the only problem brought by the centralization of bitcoin mining. In fact, there is the danger that the hardware might have a certain defect.
This would have particularly disastrous consequences if, for some reason, this defect were to occur simultaneously throughout the network. In this scenario, in fact, most of the hashrate of the bitcoin blockchain would suddenly be lost.
In general, however, this kind of problem would tend to result in economic damage to the producer due to the loss of confidence and therefore the company’s sales.
Another potential problem mentioned by Song is typical of monopolies: potential manipulation of hardware prices, the favouring of certain groups over others or the restriction of uses.
The centralisation of the hashrate
According to Song, this category can be additionally divided into two.
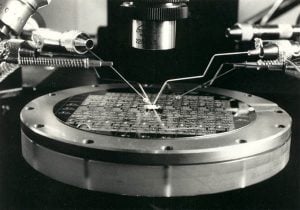
The first is the centralization of mining pools, in this case, a company controls pools that provide more than half of the hashrate to the network.
In the second case, a company directly owns (or has control over) the hardware responsible for more than half of the hashrate.

The possible attacks are not so different, but the way they are conducted is not the same.
The main difference is that in the case of pool centralization, the miners can simply change pools, whereas in the case of an entity that controls more than 50% of the hashrate this is not possible.
One thing that this kind of centralization would allow those who benefit from it, is to reject all the blocks produced by others. The consequence would be that this entity would collect all the block rewards and could censor transactions.
In addition to this they could lead to so-called double spending, as the control of most of the hashrate would be equivalent to the amount needed to execute a 51% attack successfully.
Another way to damage the network would be to turn off the mining rig: the network, besides becoming slower, would become more vulnerable to 51% attacks.
It is difficult to imagine that anyone would take this path given the economic losses that it would cause. In fact, by stopping contributing to network maintenance, the company would lose up to 1437 BTC per day.
What does the centralization of mining not entail?
The centralization of mining does not make it possible to deprive users of their BTCs. However centralized the network may become, the money is protected by the private key and, without compromising the key, it is not possible to deprive users of their funds.
It is not even possible to change the Bitcoin protocol. This, in fact, would involve a hard fork that would require everyone to update their nodes.
A further clarification: anyone with a substantial hashrate is financially exposed to the state of the blockchain in which they are involved.
Attacking the Bitcoin network thanks to hardware decreases the value of BTC. For this reason there are few potential reasons why someone, even if they could, would be motivated to conduct such an attack.



